As we enter 2023, protecting sensitive health information is more critical than ever. In 2022, the healthcare industry was the most targeted sector for data breaches, accounting for 47% of all breaches. PHI, which includes medical histories, laboratory tests, mental health conditions, and financial information, is protected under HIPAA regulations, and its standards must be followed by any healthcare business. We will help you to stay aware and informed of everything crucial in this sphere. Let’s begin!
What Is Protected Health Information?
Simply put, electronic Protected Health Information includes all patient details for easy identification and relevant treatment, plus financial info like bills and insurance. PHI covers medical history, stats, lab results, and mental health. This concept comes from the US Health Insurance Portability and Accountability Act (HIPAA) of 1996, which regulates the use of PHI.
Here is the definition of protected health information by Wikipedia:
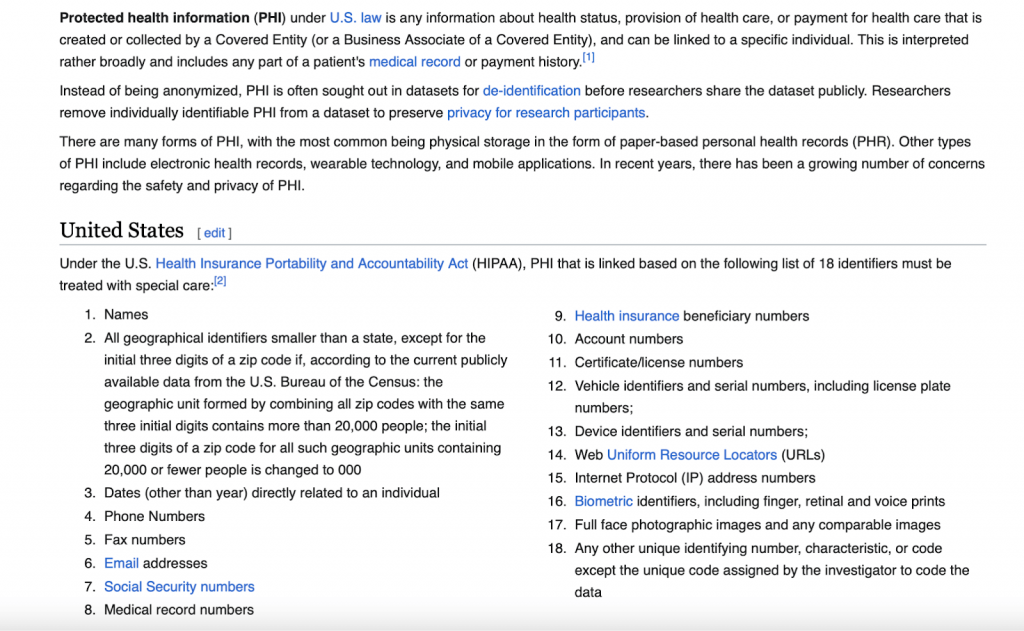
Confidential protected health information is defined by law as healthcare delivery and payment for it. HIPAA oversees how covered organizations generate, collect, transfer, and store this information. PHI includes sensitive patient details like name, address, medical history, and results. Violating PHI is illegal under federal law, and everyone has the right to keep their health information private. Managing PHI and HIPAA compliance is complex, requiring detailed reporting and strict regulatory control of Privacy and Security Rules.
Protecting the privacy of patients’ health information is of the utmost importance. It is our duty as healthcare providers to ensure that this information is safeguarded and only used for its intended purposes.”
Dr. Jane Smith
Chief Medical Officer
Do you want to ensure the confidentiality of information in your medical institution?
With ZenBit!
Electronic protected health information (ePHI)
Electronic protected health information (ePHI) refers to any PHI that is created, maintained, processed, transferred, or received through digital means. The HIPAA Security Rule outlines specific guidelines for evaluating ePHI, which can be stored on various digital devices such as internal/external hard drives, USB drives, CDs, DVDs, SD cards, and smartphones. It can also be transferred through various methods like wi-fi, internet, modem, DSL, email, or file transfer services.
HIPAA regulations are focused on protecting PHI, which makes it crucial to have a culture of managing PHI to achieve compliance. However, certain data elements such as payments, IP addresses, retina scans, fingerprints, diagnostic codes, and visit dates are often overlooked.
It’s important to note that protected health information also includes historical information, such as an old address or phone number, which can still be used to identify an individual. Therefore, PHI is a concept that lies between an identifier and health data.
How to Engage with Confidential Protected Health Information
PHI is a sensitive type of information that needs to maintain the privacy of patient’s medical records. PHI can be in the form of electronic (ePHI), written, or verbal communication. The privacy standards for all types of PHI are the same, and it is crucial for every employee whose job involves accessing PHI to be aware of how to interact with it. A tiny mistake or miscue can lead to a data breach or destruction of protected health information which can have severe consequences for both the patients and the organization.
To manage PHI effectively, employees must adhere to the minimum necessary standard. This standard requires them to use the least amount of PHI necessary to perform their job functions. It is also essential to keep the information accessed confidential and not disclose it to anyone, including colleagues unless it is necessary for them to know. Professionalism and prudence are crucial when dealing with PHI, regardless of whether you belong to the IT staff, health plan administrators, HR representatives, accounts payable, or business owners.
If an employee notices protected health information (PHI) being revealed in their department, it is their responsibility to inform the security officer immediately. Reporting any suspected data breaches or incidents can help minimize the damage caused by the breach and prevent similar incidents in the future. Additionally, organizations must provide regular training to employees on the proper handling of PHI and the privacy standards that apply to it. This can help ensure that everyone is aware of their responsibilities and can take the necessary steps to protect PHI.
HIPAA Compliance Remains The Top Importance In 2023
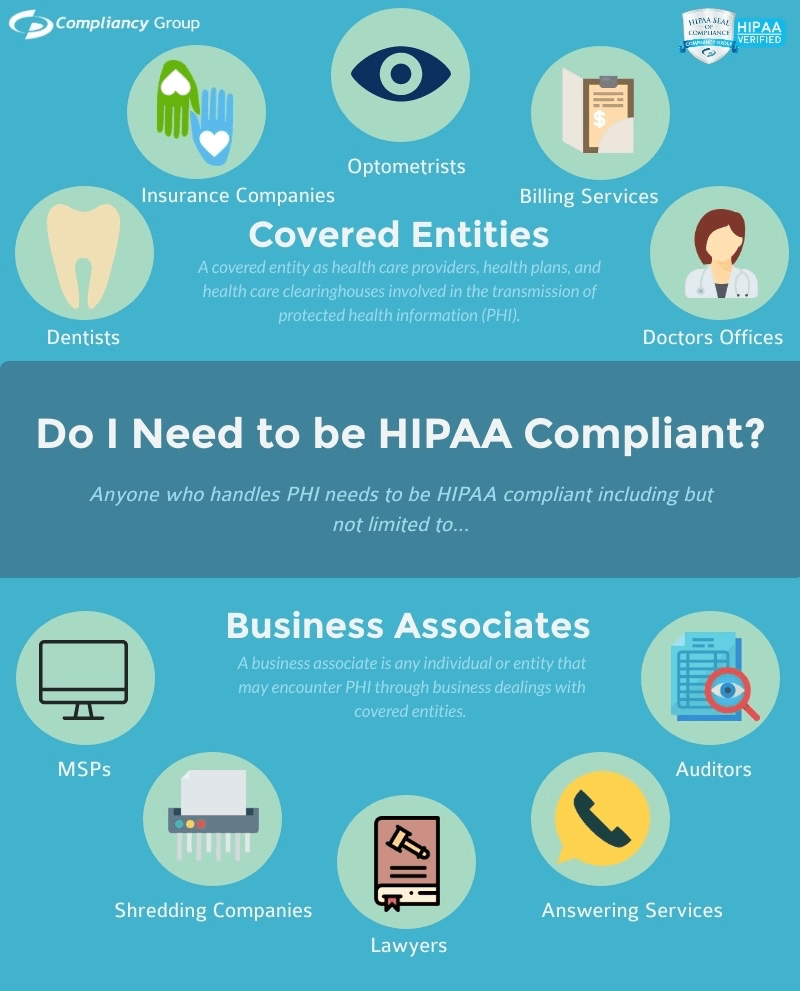
HIPAA compliance is a critical requirement for all covered entities, including healthcare providers and organizations that offer health insurance plans to their employees.
As a healthcare company, we take our responsibility to protect our patients’ protected health information very seriously. We have implemented robust security measures and trained our staff on HIPAA regulations to ensure that patient privacy is maintained at all times.
John Doe
CEO of XYZ Healthcare
HIPAA Violation Consequences
Violating HIPAA law can result in penalties for both employees and employers. The Office of Civil Rights can sue businesses, and individuals may face hefty fines ranging from $100 to $250,000 or up to ten years of imprisonment. In the image below we show the main types of HIPAA measures:
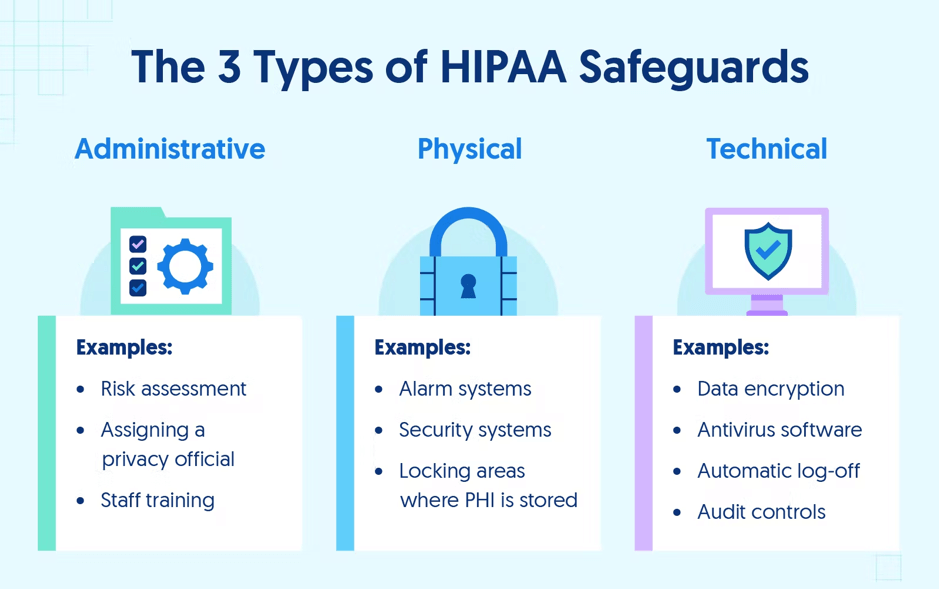
HIPAA protective measures are designed to ensure PHI’s confidentiality, integrity, and availability. Administrative safeguards involve implementing policies and procedures to manage the security of PHI, physical ones include controlling access to physical locations containing PHI, and technical measures involve implementing security tools to protect PHI that is transmitted electronically. All this helps to prevent unauthorized access to PHI and maintain its privacy.
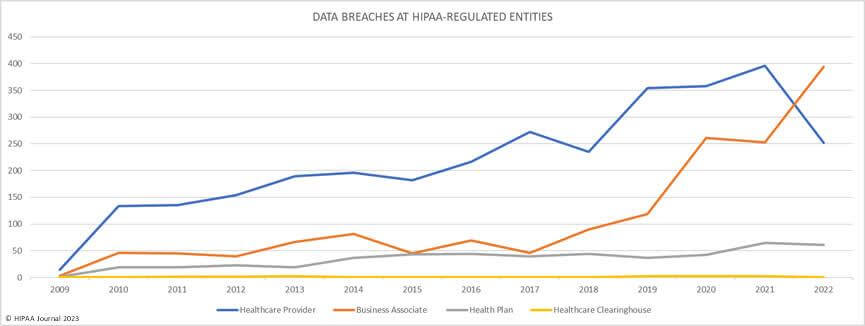
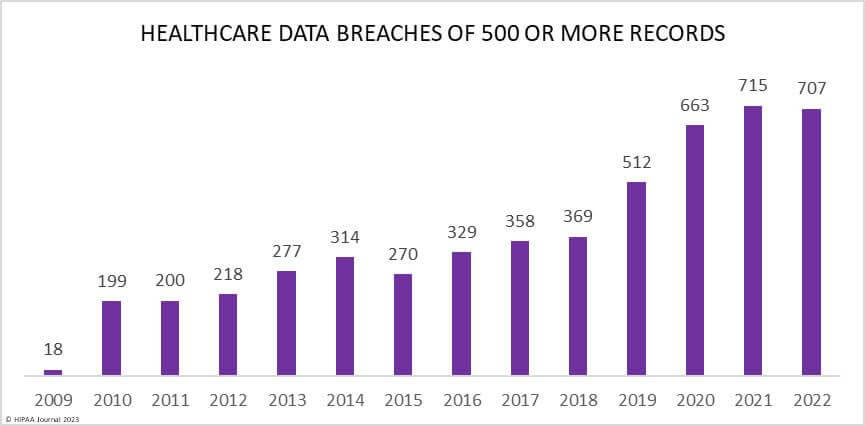
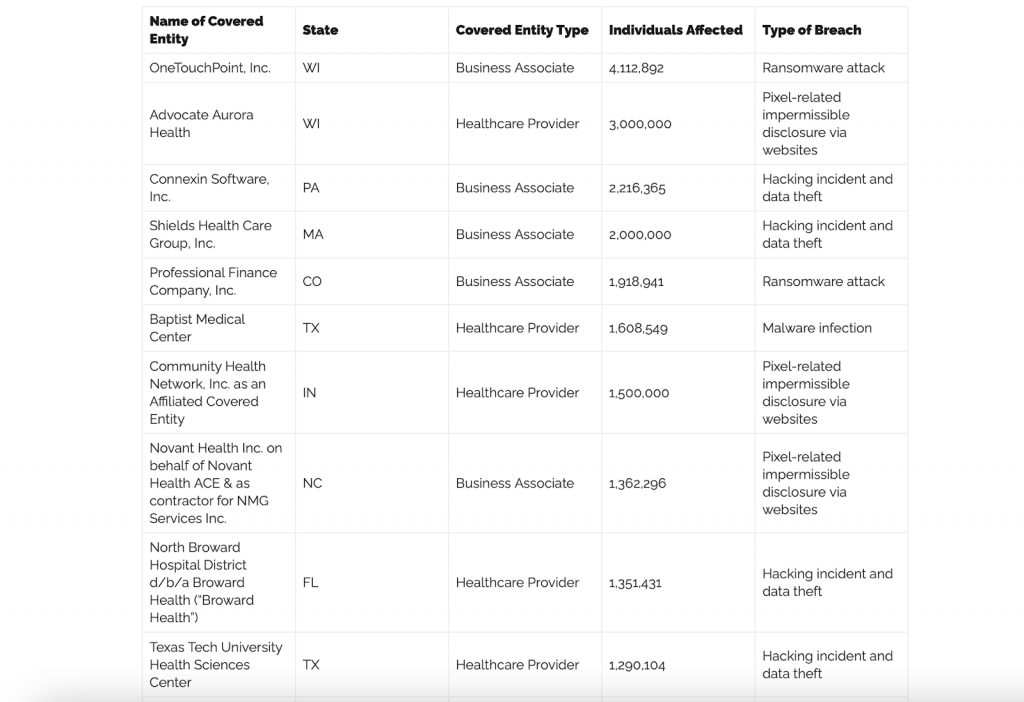
In 2022, more than 10 healthcare data breaches were reported, each affecting over 1 million records. The majority of these breaches were caused by hacking incidents, often involving ransomware or attempted extortion. However, several incidents of impermissible disclosure resulted from the use of pixels on websites.
These tracking technologies, which were added to improve website functionality and services, inadvertently collected electronic protected health information that was transmitted to third parties like Meta and Google when users visited the websites while logged into their Google or Facebook accounts. Healthcare organizations’ widespread use of these tracking technologies prompted the OCR to issue guidance, highlighting the considerable potential for HIPAA violations.
To prevent serious consequences, HIPAA requires companies dealing with PHI to establish sanction policies. Depending on the severity of the violation, sanctions may include suspension without pay, letters of reprimand, and/or termination of employment.
Sharing Private Health Information with Close Contacts in 2023
While medical professionals are legally obligated to protect the privacy of the data they handle, it is possible to share PHI with relatives and friends with the individual’s consent. There may be situations where this is necessary, such as having a family member pick up test results or a prescription. Or if a patient is unconscious or incapacitated. This is the case where family or close friends can help greatly in the best interest of the patient and the information shared is directly related to the person’s involvement in the patient’s care or payment for healthcare services. This is known as the “incapacity exception” and helps to ensure that patients receive the necessary care and support even when they are unable to make their own decisions. Additionally, a physician may discuss a patient’s condition, treatment, and bills in the presence of their spouse.
Nevertheless, individuals have the right to object to the discussion of their current health state with anyone if they do not wish to disclose the information to. It is important to communicate any objections clearly to medical professionals to ensure that the privacy of PHI is maintained.
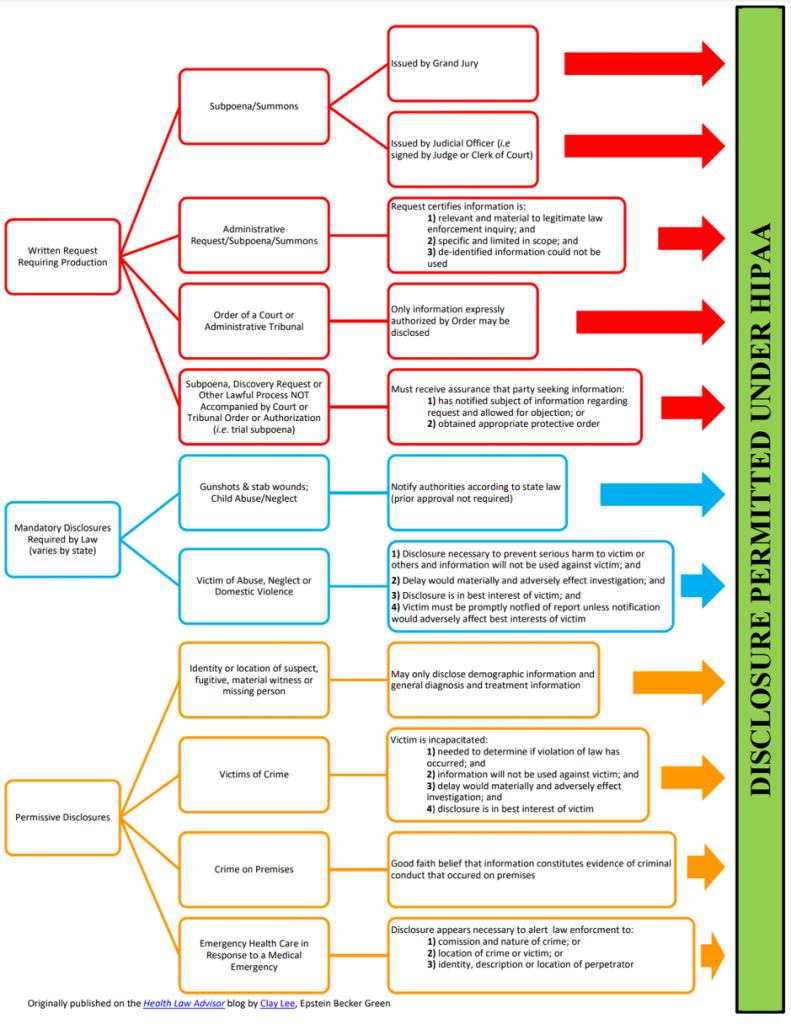
Talking of permissions, HIPAA permissive disclosures are situations in which an individual’s protected health information can be shared without their explicit authorization. Examples include disclosures for treatment purposes, payment, and healthcare operations, and disclosures required by law or public health activities. However, covered entities must still follow HIPAA’s privacy and security rules when making permissive disclosures.
Some advice on how to protect health information
When it comes to handling Protected Health Information, it’s always better to be safe than sorry. One way to make sure your work data stays secure is by following a clean desk policy. That way, you can be sure that your patient’s information is in good hands.
Let us give you some tips to keep your company’s data safe!
- Lock your computer: Always lock your computer screen when you step away, even if it is just for a few minutes. This is especially important if you are in a shared workspace or have visitors around. To lock your computer, use a password-protected screensaver or simply press the “Windows + L” keys. This will ensure that nobody can access your computer or sensitive information without your permission.
- Store files in a secure place: Sensitive documents and files should be stored in a safe and secure location. A locked filing cabinet or a secure room with limited access is a good option. If you need to work with sensitive information on a regular basis, consider using encrypted file storage solutions. This will help ensure that your files are protected even if they fall into the wrong hands.
- Follow company policies and procedures: Make sure you read and understand your company’s policies and procedures regarding data security. If you have any questions or concerns, talk to your supervisor or IT department. Adhere to the guidelines set by your company, even if it means putting in some extra effort. This includes things like changing your password frequently, avoiding public Wi-Fi networks, and reporting any suspicious activity to your IT department. Remember, PHI-protected health information security is everyone’s responsibility, and following company policies and procedures is essential to prevent data breaches.
Electronic Protected Health Information And Health Apps
Have you ever wondered if the health app you’re using is keeping your sensitive data safe and secure? It’s a valid concern since health apps collect a lot of personal information that needs to be protected. Unfortunately, there’s no guarantee that all health apps follow HIPAA rules, which can make things pretty chaotic when it comes to PHI and health apps.
For example, health apps can track everything from your weight and daily physical activities to your location, diet, and other identifiers. But even if your doctor recommends a health or fitness app, the data you share with it may not be protected by HIPAA standards.
There are a few things you can look for when selecting a health app to help ensure your data is protected:
- Check for privacy policies: Look for apps that have clear, easy-to-understand privacy policies that outline how they collect, use, and protect your data.
- Research the developer: Look for apps developed by reputable companies or organizations that have a track record of strong data protection practices.
- Look for encryption: Encryption is a method of protecting data by encoding it so that only authorized parties can access it. Look for apps that use encryption to protect your data.
- Read reviews: Check user reviews and ratings for the app you are considering. Reviews can provide valuable insight into the app’s user experience and data protection practices.
- Consider app permissions: Be aware of the permissions you are giving the app when you download and use it. Make sure the app is only accessing the data it needs to function and that you are comfortable sharing that data with the app.
Remember, while there may not be a perfect solution when it comes to data safety in health apps, being cautious and doing your research can help you make more informed decisions about which apps to use.
Ensuring the confidentiality of patients’ protected health information is not only a legal requirement but also a critical component of building and maintaining trust with our patients. We must be diligent in our efforts to protect this information and ensure that it is only accessed by authorized individuals.
Dr. Sarah Johnson
Medical Director of ABC Clinic
Respect And Act In Accordance With Rules
At the end of the day, following HIPAA rules for managing Protected Health Information is essential for protecting your business’s reputation and avoiding potential penalties.
At ZenBit, we understand the importance of dealing with sensitive health information and being HIPAA-compliant. It’s a top priority for any business that deals with PHI, and we have the expertise to support you in this area. We know that your reputation and customer service are critical, and we are committed to helping you maintain both.
Our team of developers provides strategic advice and decision-making support for incorporating emerging technologies into your business for steady growth. We offer valuable connections, insights, and a competitive edge to our clients. Our approach to research focuses on both primary research and our vast global network.
So, if you’re looking for expert support in protecting your business’s reputation and complying with HIPAA rules, contact ZenBit today for more information!
- FAQ
- What qualifies as protected health information (PHI) under HIPAA?
PHI is any individually identifiable health information that is created, received, stored, or transmitted by a covered entity or business associate. This includes information such as a person's name, address, birth date, medical history, test results, and other health information that can be used to identify an individual. PHI can be in any form, including electronic, paper, or oral communication.
- Is it permissible for healthcare providers to allow members of the media, including film crews, into treatment areas of their facilities without obtaining prior written authorization?No way. They are not allowed to let media personnel, including film crews, into areas of their facilities where patients' private health information (PHI) could be seen, heard, or accessed. That's right - written permission is needed from each individual whose PHI will be accessible to the media, whether it's in written, electronic, oral, or another visual or audio form. Now, there are some rare situations where HIPAA rules allow PHI sharing with the media without prior authorization from the patient. But these cases are very limited and carefully outlined in the rules. So, in general, your private data should stay private and protected from prying eyes!
- Does the HIPAA Privacy Rule cover genetic information?The answer is a resounding yes! Genetic information falls under the category of health information protected by the Privacy Rule, just like any other health-related data. However, for it to be considered protected, it must meet the definition of protected health information - which means it must be identifiable to an individual and be kept by a covered healthcare provider, health plan, or healthcare clearinghouse. So rest assured, your genetic info is safe and sounds under the HIPAA Privacy Rule!