This article is our humble commitment to the healthcare community. Cybersecurity in Healthcare is vitally important nowadays, and we are delighted to share some of our knowledge and experience in this field. As all data becomes digital and is stored in the cloud, we will help you to get the picture of cybersecurity aspects in the world of healthcare and how to create a safe environment in practice.
Why Cybersecurity in healthcare is Important
No need to convince you that cybersecurity matters a lot as well as the culture of caring about it. The software and hardware, cybersecurity ethics, and cyber hygiene come as a unity and their protection and constant improvement should be treated with respect by all members of the staff otherwise it can lead to lawsuits and penalties, spoiled brand reputation, and patients loss.
To make a clear understanding of cybersecurity risks possible, we have no choice but to study the laws and penalties that apply. In the USA they are getting more and more strict and include both well organized cyber crimes and neglect on purpose. So, the impressive number of 1,5 million dollars is the highest annual fines for mistreatment. Quite enough for security updating motivation, isn’t it?
The situation with penalties in the Eurozone is not only pretty much similar but even tougher. Personal and health information is managed by The General Data Protection Regulation and the penalties for data breach per year can reach up to 20 million euros. Breaking security laws is not only expensive but extremely stressful as well due to public shaming.
Besides, on the black market healthcare data can have unbelievably high value – $500 US for a single file seems not a bad benefit at all, and a healthcare system contains thousands of such documents that include sensitive personal and health information.
According to Becker’s Hospital Review, the hospital news magazine, the healthcare industry loses around 5.6 billion USD every year due to data breaches which are quite shocking.
Cyber attacks on hospitals cases
Apart from data theft healthcare organizations can face other threats such as critical IT infrastructure control when the attacker accesses medical devices or physical systems and cuts the power supply off causing a disaster.
We would like to mention here two real dramatic cases of a cyberattack – the WannaCry and the AMCA hacking data breach cases.
The first one dates back to the spring of 2017 when Microsoft Windows spread the WannaCry ransomware and in a couple of days thousands of NHS medical centers across the United Kingdom got into trouble being unable to access vital data. The experts say with better protection and users’ culture it could have been possible to prevent the damage. The WannaCry case is a perfect example of ransomware vs payment topic. Although the victims’ fears and pressure are understandable in this situation, it is strongly advised to stay calm and avoid paying hackers as there is no guarantee it will start working again. The WannaCry hackers received their money but due to the faulty coding, it turned out impossible to regain data access. Some researchers reported that the data was permanently lost, others claim that some victims did find it. Anyways, thousands of computers damaged, canceled appointments, billions in losses across the globe, ambulances failing to come to people in need is terrifying enough to understand the importance of updating digital security measures.
The other drama lasted for about a year when the vital data of 25 million patients was compromised. The AMCA’s systems data breach happened in the late summer of 2018 damaging clinical laboratories, laboratory testing businesses, and healthcare providers. The American Medical Collection Agency is a company that provides billing and collection services for many large organizations in the healthcare sector. The data breach in AMCA led to huge client loss, state investigations, and lawsuits. AMCA has filed for bankruptcy protection. Cybercriminals took advantage of using credit card information for money theft as well as from online cheating and blackmail.
Healthcare data breaches examples
There are several well-known situations when data breaches can happen and we will mention them all here so that you are armed enough to identify a potential data breach beforehand and understand the importance of a cyber hygiene routine.
Actions that are not supposed to happen or their lack when needed are treated in a security context like human error. Either employees or healthcare system clients can be a reason for the misfortune that is not always innocent. The wrong document attached to a newsletter, private sensitive data sent or handled to the wrong addresses, etc. Very often human error occurs when a person is developing the habit of taking shortcuts to save time and make their job routine more effortless. Data breaches due to human error are most numerous and in some companies reach up to 90% which cries for urgent improving cybersecurity culture.
Cybercriminals are external hackers, usually working in teams, who access a network for stealing personal data or secret company information and demanding huge financial rewards. They have their underground markets with various specializations polished to perfection and is a real challenge to find and arrest such a king of criminals, laws related to it are constantly improving worldwide.
Worms and viruses, ransomware and spyware, Trojan viruses, etc go to malicious software. No need to explain what damage and disruption it does to your digital system as the necessity to protect it with the best available antivirus software possible. It’s better to regularly invest money in computer protection than one day become a victim of dangerous ransomware that will block access to computers or data and only with payment it is possible to unblock. This is the case when hackers get huge financial benefits and companies fail.
When sensitive data is left without any protection like security measures or at least a decent password we have a misconfiguration case. It may be regarded as a preferred easy target for hackers, and the harm they do to companies is often close to catastrophe. For example, Teletex huge data leakage two years ago when more than 500 thousand files were lost. The reason was Amazon Web Service misconfiguration. The other types of insecure configuration include unpatched systems, unencrypted files, web applications that are out of date, default account settings, etc.
Social engineering is a common way to manipulate individuals. Employees get tricked by, for instance, phishing attacks – pretending to be someone honest and reliable like a credit card brand, the hacker gets all the personal information he needs.
Hackers use smart tricks to fool employees and persons responsible for the company’s precious information. They become victims of psychological manipulation since the malicious email received calls upon fear, guilt, or urgent necessity. They often seem innocent like some special invitation advisory, incoming fax, service cancellation, shipping document, delivery confirmation, healthcare reform laws, etc. It is enough to open an email or click on the link and the attack is initiated. Unfortunately, the attacks are extremely common and unbelievably professional nowadays.
Privileged misuse has a lot to do with medical ethics and happens when the information is used not the way it is supposed to. The guilt here is on one of the staff members who possess legal access to the data and copies it, mishandles or shares it with the wrong people. The storyline is typical, bad access control usually leads to privileged misuse. Employees have more access rights than needed to do their jobs, and the company authorities can’t monitor every step of privileged accounts.
Physical intrusion is the stealing of data either on paper documents or stored in phones, laptops, or disks.
There are high-tech, low-tech, and no-tech security levels. In the case of no tech, it is enough to get into the building and the chance to steal is already open since people around minding their own business and are not suspicious. The nurses’ station is a good target place, it does not take a lot to take a picture of a medical record or doctor’s contacts. Healthcare is very fragile and, in most cases, data breaches come from a mad or unhappy ex-employee. In this very tight and dynamic healthcare process with a lot of people involved, employee separation is the way to data security.
Types of healthcare data
The two different types of data require correct understanding and proper managing. Name, surname, date of birth, home address, phone number, and e-mail address is what we call personal data of course. It also includes a special category which is treated with extra care – sex life, racial origin, married or single, criminal records, religious beliefs, political views, etc.
Consequently, health data is everything related to the health status of a patient. Laboratory tests, diagnoses history, prescriptions, examination reports, and other medical information which goes together with the administrative and financial healthcare part including invoices, appointments timetables, important medical certificates, etc.
Both types of patient data are highly sensitive and only professionals obliged to medical secrecy can have access to it.
Health Data Processing
How can you be sure that you process health and personal data in the right way? According to medical ethics rules, the patients’ data processing should be mutually agreed upon. When a patient is no longer in a hospital or the treatment was paused, the document must be signed for further data processing.
This is one of the points from the checklist of gathering and processing.
Cybersecurity and information security are continuous processes that everyone should contribute to. We prepared the checklist of crucial points that can help healthcare staff members see whether they are acting accordingly.
To begin with, the data must correspond to the medical treatment precisely and be handled by the professionals who commit the duty of medical secrecy. The patient should have a clear knowledge of his data details being processed and why. There is a retention period of keeping data and it has to be respected as well. It has to be possible for a patient to access his or her private data file and put changes when needed. Confidentiality declaration should never be ignored. In case of suspected danger, proper safety measures are to be provided.
Of course, building data security in healthcare is not a matter of one day and it depends both on the medical organization policy and each staff member. According to medical ethics and professional standards, it is not acceptable to talk about patients either in public or via social media posts. The personal computer should be locked and account information remains private. Important documents and patients’ files cannot be openly accessible in any way. Workplace rules should be obeyed and technical support available when needed.
Healthcare Solution Compliances
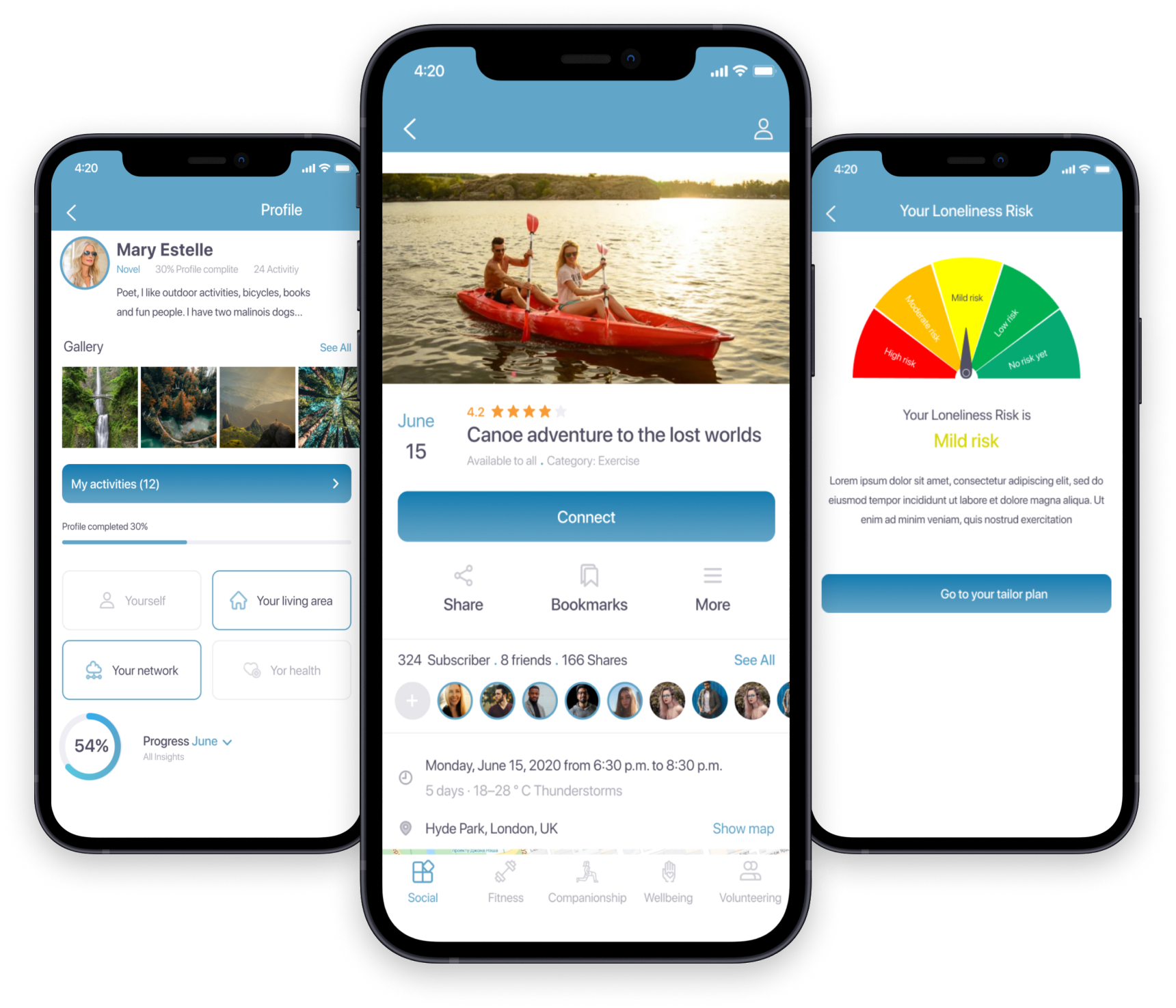
Also, compliance with such requirements as HIIPA, GDPR, FDA and others is very important for healthcare applications. We are proud of EvZein aged care software’s key features. To begin with, product is a GDPR compliant app. Since they store private and health data, the EU’s General Data Protection Regulation law makes it consistently safe. GDPR requirements apply to everyone in the European Union, and some of the most important ones include data breach alerts, collected data anonymizing, different consents demands for data processing, safety in data handling, etc.
If the security compliance of your healthcare product is also important to you, then you can learn by example how we handled this by reviewing our client’s case study below.
Cyber hygiene
Cyber hygiene is like personal hygiene. Our daily routine keeps us fit and safe so digital information practices should be treated with the same respect and devotion to keep sensitive data safe and protected.
- Digital communication and safe emailing
The Breach level index points out a number of more than 13 million cybersecurity breaches during the last decade. What is shocking in that research is that 96 percent of the data weren’t prevented by a code. Of course, it is the email method that cyber hackers use mostly. Being an age-old limited technology emails are very insecure. Advanced companies use modern team communication platforms such as Mattermost, Discord, Slack, etc. However, security researchers put a lot of their skills and efforts to improve email service and safety.
Consider the following policies in healthcare processes, they are your primary concern in safety guidelines and protection.
First of all, there must be no doubt that the addressees of your data are who they claim to be. The patient’s sensitive personal information shared with the doctors and nurses involved in his recovery process is one case. The same refers to his financial information that is going to be shared with suppliers and even relatives or friends.
Make sure your information is shared via communication channels that are private, reliable, and hard to penetrate. It’s normal to be choosy before buying an app, they are all claimed secure but in reality, it is different. Investigate their reputation, test, and compare, it will give you much confidence.
Staff members’ cyber hygiene education is important. If every medical professional is aware of the different dangers and consequences, confidential and login information will be protected more.
Let’s not forget about VPN and its safe pathway through which your data can be shared online. It is like using a private server. Choose carefully, VyprVPN and IVPN seem to be the best options. And never click on short links in emails because you cannot predict where they will lead you. And be careful of links that have too many subdomains, as they could contain wicked code or ransomware. Check whether a link is malicious or not.
Devices left without proper attention can be stolen. No matter how simple and obvious it may sound, we feel responsible to mention that as well.
Working place should be locked every time you leave otherwise an unwanted guest may harm. Never plug into devices you do not know and do not trust. It is common to use a USB to activate an attack, no matter how innocent the reasoning may sound. The latest updates and patches is a security must have. Healthcare devices deserve this kindness from their owners. Do not ignore security notifications and warnings even if you are already bored with them.
Using strong passwords is no doubt common knowledge nowadays but remember to change them often, this is a great habit for data safety.
You will worry less with a password manager knowing that there is a unique password for every account. RoboForm, NordPass, Keeper, and many others are available for different operating systems and devices.
Although sharing passwords endangers your account protection greatly, even healthcare professionals have this bad habit and it is a reason for great concern for medical organizations. Shared data at some point fall into the wrong hands and bigger crime in the digital system is already on its way.
The longer the password is the better, the more sophisticated, the better, it should have eight characters at least and diversity – usual lowercase letters should be accompanied with the capital ones, numbers and symbols. Hackers should face a real challenge when trying to break it.
- Software, updates, and backups
Cybersecurity software is more than just one tool, like antivirus but a set of interconnected tools for protecting your data and devices from the many different dangers out there. Apart from password manager and VPN which we have already mentioned, there are Firewall software, credit and dark web monitoring, data breach notifications, etc.
Backups in healthcare are vitally important as in case of a data loss due to a cyber attack they can save someone’s life.
We kindly ask you to encrypt your data. Be careful when using different types of connections, the safest ones are only appropriate in healthcare.
Conclusion
There are no perfect systems and digital vulnerability in healthcare data exchange is not an exception. Luckily it is still possible to make gaining access to your communication less easy. Cybercriminals’ targets are weak and non-encrypted systems, as a rule, and criminals threats, unfortunately, continue to evolve. To stay ahead, healthcare professionals must improve culture and awareness about what is going on to help to safeguard patient data. We hope our study of data breaches in healthcare and how to prevent them was helpful and from now on it will cost much effort for the hacker to steal your data. Please be safe.
Find out how else you can protect your healthcare product from our cybersecurity specialist in the block below.
DevOps as a ServiceDevOps on autopilot
CTO as a ServiceStregthen your team
Software testingEnsure software quality
Discovery phasePlan your priduct from a to z
Cloud ServicesGeneral information about healthcare cloud services
Google Cloud ServicesEnsuring confidentiality when working with medical systems
AWS Cloud ServicesServices specially designed for the healthcare industry
Microsoft Cloud ServicesPlatform processing, analyzing and sharing medical data