2021 was a record year in terms of the number of data breaches. According to Cybercrime Magazine, ransomware costs are foreseen to reach 265 billion USD by 2031. The experts predict every new attack within 2 seconds interval, and this is the main takeaway so far since the number of cyber threats becomes secondary compared to alarming consistency in targeting.
Providing vital services and dealing with the most sensitive high-value data, the healthcare sector has always been an attractive spot for cyber threats, if not a gold mine, as any data breaches here may lead to dramatic outcomes. No wonder, cybercriminals keep looking for new ways to disrupt the industry for their potential benefit is worth the effort.
Healthcare providers give great importance to security measures. Let’s talk about the potential cybersecurity challenges in using iot in the healthcare industry and how definite steps will make your cybersecurity health stronger.
The main protective role belongs to the Health Insurance Portability and Accountability Act (HIPAA). The prime laws help to control how well healthcare institutions implement proper security measures to keep patient data safe.
Knowledge is crucial here. Hackers can threaten from lots of spots, the criminal locations may be either inside or outside the healthcare company. Doing your best in your own cybersecurity practice, keep in mind the risks coming from outside, if you are aware of them, you are stronger and always alert. It is also worth mentioning that the approaches healthcare professionals use, aiming to protect their patients’ sensitive data, are drawn-out enough.
IoT healthcare cybersecurity main dangers
We did a little investigation and compiled a list of the top healthcare cybersecurity challenges that will help you in building a strong and safe cyber security business environment. So let’s get started!

Pay attention to the emails
The most “innocent” ones are perhaps Phishing attacks when an employee is tempted to reveal important personal information without any suspicion as the email with requests comes from his bosses or colleagues from other departments. It may be an urgent demand to change passwords or share the needed billing info or patients’ private data, etc. Only a well-trained user is able to ring a bell on these phishing emails. As innocent as they seem, these attacks may lead to HIPAA compliance violations or lawsuits connected to data exposure.
Cloud storages are not always safe
Though cloud-based healthcare solutions have become popular among providers like SaleceForce, Ama Web Service, Kinvey, Dropbox, IBM, etc, this kind of storage is not always following HIPAA standards, sadly.
Data encryption is crucial here before data cloud transferring, in fact, the private cloud data center is a perfect solution here. To have your own safe place for precious data and its consistent encryption routine.
Warning! Unhappy ex-employee
Healthcare staff negligence has its opposite. Insider sabotage comes from someone disgruntled on purpose within a company, no matter if it is a current employee or business partner or the one who quit the workplace years ago. The black market is full of money and having employees as partners works perfectly as no one on the street may know exactly how a network is set up, its passwords and weak points, etc. When having to deal particularly with this issue, providers fully realize why zero-trust access and data encryption policy is crucial to cybersecurity.
Ransomware as the most dangerous threat
Though Ransomware dangers have been known for decades for costing lots of time and money, the newly appeared Ransomware as a Service (RaaS) is making them even more powerful.
The whole process is shamefully simple. The hacker affects the company’s OS with malware that encrypts protected health information (PHI) with no hopes for further access. And of course, there is no other way to recover the access but pay the cybercriminal via some difficult-to-trace money transfer method like Bitcoin, Stellar, Litecoin, etc. Moreover, having regained access is not the reason to celebrate as there is always a chance of PHI duplication.
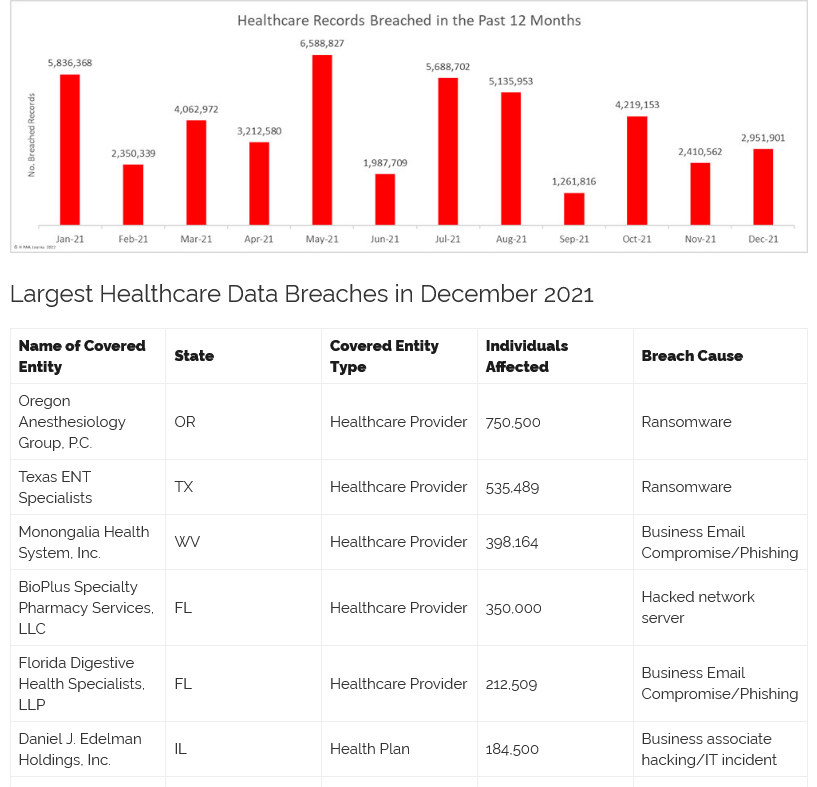
The COVID-19 reality has put a new color on this threat. Lots of ransomware emails come under the masks of trustworthy institutions like government advisories, healthcare consultants, etc. According to the Mimecast study, 2021 can be named as the year of ransomware with 80% of businesses threatened globally, and around three thousand ransomware attacks over the last two years. The US victimized businesses’ average ransomware payment was more than 6 million USD worth.
Ransomware cyber threats may, sadly, lead to lethal consequences during a forced slowdown in a hospital workflow. That’s why it is vitally important to focus on powerful backup planning so that, in case of a cyber attack, key information will remain available. In this case, patients with urgent care needs are more protected.
Data breaches victim industry number one
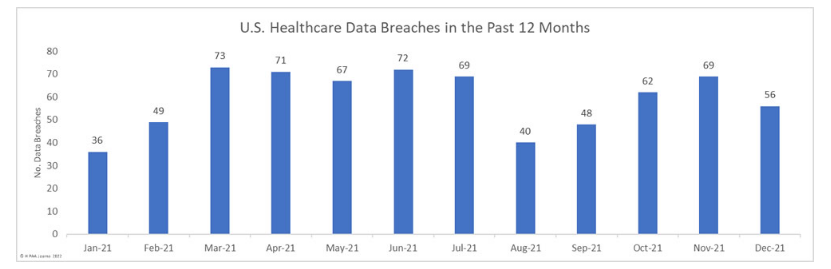
The Healthcare is a number one data breaches victim industry, sadly but the reason behind it is very easy to understand. In 2021, 59 data breaches per month were recorded as average, and 712 healthcare data breaches during the whole last year, which sets the new record, unfortunately. Anyways, the alarming numbers show how much we need to aim for perfect device usage to protect PHI, it stands in the same line with medical care indeed.
There is a gap between HIPAA requirements being nicely established in healthcare practice, and the possibility to be closely connected with current security measures, documentation, and a cool IT department. This is the weak spot where cybercriminals target eagerly causing troubles.
One more important challenge to be aware of
We would like to finish our list with Distributed denial-of-service (DDoS) attacks. They are connected to Internet traffic in your company network. Cybercriminals try to overload it with crazy amounts of fake data so that the system fails to function well. These attacks are very harmful, especially in urgent care cases. Filing the prescriptions becomes impossible as well as accessing medical test records and other important healthcare activities.
If the safety of your healthcare IoT solution is also important to you, then you can describe your problem to our cybersecurity specialist in the block below.
Conclusions
Being increasingly digital, modern medicine and healthcare remain fragile and open to cyber threats, and there are no hints on them to slow down. From phishing attacks, suspicious websites, misleading websites to devil ransomware, it is not easy to protect sensitive data at all. Cybersecurity is blanketed with much attention and big money as every serious business cares about its reputation and sharing the best experience with patients who trusted them.
When engaging in cybersecurity matters in your practice, it is important to develop a cool IT infrastructure, train staff to blindly follow a privacy-conscious style of data managing, and the software should be implemented properly. The new security software should be both effective and simple to use.
For ZenBit developers cybersecurity is essential when it comes to product design. We keep working with our clients during the maintenance stage to make sure safety measures are powerful, and the company’s PHI, money and reputation are being protected in the best way possible. You are welcome to contact us any time. Take care and see you soon!